Intel chips Vulnerability
A vulnerability in Intel chips that went undiscovered for almost a decade allows hackers to remotely gain full control over affected Windows PCs without needing a password.
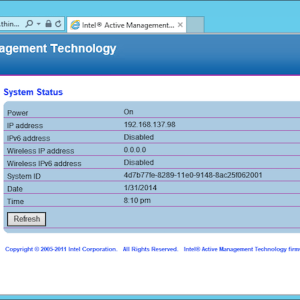
The “critical”-rated bug, disclosed by Intel last week, lies in a feature of Intel’s Active Management Technology (more commonly known as just AMT), which allows IT administrators to remotely carry out maintenance and other tasks on entire fleets of computers as if they were there in person, like software updates and wiping hard drives. AMT also allows the administrator to remotely control the computer’s keyboard and mouse, even if the PC is powered off.
To make life easier, AMT was also made available through the web browser — accessible even when the remote PC is asleep — that’s protected by a password set by the admin.
The problem is that a hacker can enter a blank password and still get into the web console, according to independent technical rundowns of the flaw by two security research labs.
Embedi researchers, credited with finding the bug, explained in a whitepaper posted Friday that a flaw in how the default “admin” account for the web interface processes the user’s passwords effectively lets anyone log in by entering nothing at the log-on prompt.
“No doubt it’s just a programmer’s mistake, but here it is: keep silence when challenged and you’re in,” said the researchers.
Tenable researchers confirmed the findings in a detailed analysis of the flaw, also posted Friday, saying it was relatively easy to remotely exploit.
Intel’s advisory said that systems — including desktops, laptops, and servers — dating back as early as 2010 and 2011 and running firmware 6.0 and later are affected by the flaw.
But Embedi warned that any affected internet-facing device with open ports 16992 and 16993 are at risk. “Access to ports 16992/16993 are the only requirement to perform a successful attack,” said the Embedi researchers.
![]()

