The Port Scan Attack Detector (PSAD) is a lightweight system daemon that is designed to work with Linux iptables/firewall code to discover suspicious traffic such as port scans, backdoors, botnet command and control communications, and more. It includes a set of vastly configurable danger thresholds, long-winded alert messages that comprise of the source, destination, scanned port range, begin and end times, TCP flags and equivalent nmap options, reverse DNS info, email and syslog alerting, automatic blocking of offending IP addresses via dynamic configuration of iptables rulesets, passive operating system fingerprinting, and DShield reporting.
Features
- Detection for TCP SYN, FIN, NULL, and XMAS scans as well as UDP scans.
- Support for both IPv4 and IPv6 logs generated by iptables and ip6tables respectively.
- Detection of many signature rules from the Snort intrusion detection system.
- Forensics mode iptables/ip6tables logfile analysis (useful as a forensics tool for extracting scan information from old iptables/ip6tables logfiles).
- Passive operating system fingerprinting via TCP syn packets. Two different fingerprinting strategies are supported; a re-implementation of p0f that strictly uses iptables/ip6tables log messages (requires the –log-tcp-options command line switch), and a TOS-based strategy.
- Email alerts that contain TCP/UDP/ICMP scan characteristics, reverse dns and whois information, snort rule matches, remote OS guess information, and more.
- When combined with fwsnort and the iptables string match extension, psad can generate alerts for application layer buffer overflow attacks, suspicious application commands, and other suspect layer 7 traffic.
- Icmp type and code header field validation.
- Configurable scan thresholds and danger level assignments.
- Iptables rule-set parsing to verify “default drop” policy stance.
- IP/network danger level auto-assignment (can be used to ignore or automatically escalate danger levels for certain networks).
- DShield alerts.
- Auto-blocking of scanning IP addresses via iptables/ip6tables and/or tcpwrappers based on scan danger level. (This feature is NOT enabled by default.)
- Parsing of iptables/ip6tables log messages and generation of CSV output that can be used as input to AfterGlow. This allows iptables/ip6tables logs to be visualized. Gnuplot is also supported.
- Status mode that displays a summary of current scan information with associated packet counts, iptables/ip6tables chains, and danger levels.
Visualizing Malicious Traffic
psad offers integration with gnuplot and afterglow to produce graphs of malicious traffic. The following two graphs are of the Nachi worm from the Honeynet Scan30 challenge. First, a link graph produced by afterglow after analysis of the iptables log data by psad:
![alt text][nachi-worm-link-graph] [nachi-worm-link-graph]: images/nachi_worm.gif “Nachi Worm Link Graph”
The second shows Nachi worm traffic on an hourly basis from the Scan30 iptables data:
![alt text][nachi-worm-hourly-graph] [nachi-worm-hourly-graph]: images/nachi_worm_hourly.png “Nachi Worm Hourly Graph”
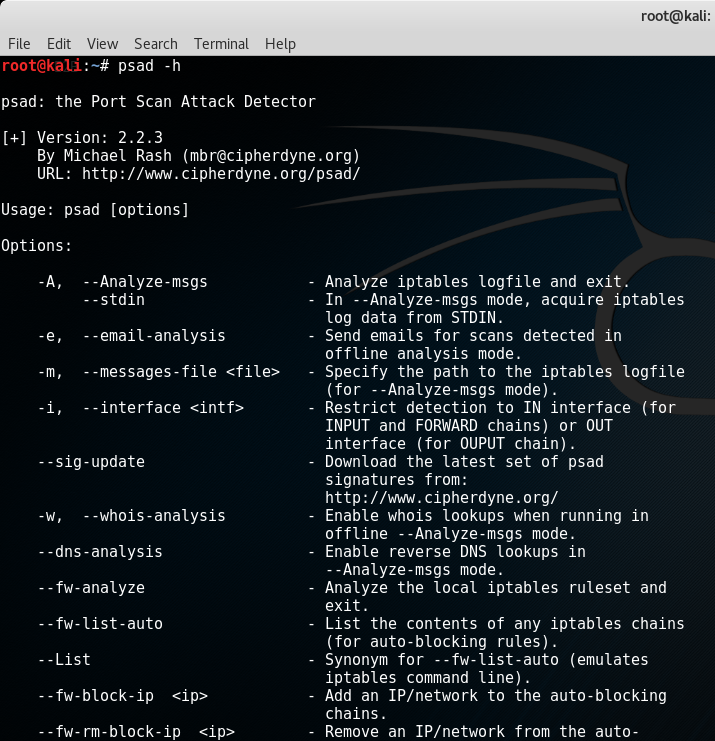
Installation
Depending on the Linux distribution, psad may already be available in the default package repository. For example, on Debian or Ubuntu systems, installation is done with a simple:
apt-get install psad
If psad is not available in the package repository, it can be installed with the install.pl script bundled in the psad sources. The install.pl script also handles upgrades if psad is already installed. psad requires several perl modules that may or may not already be installed on your Linux system. These modules are included in the deps/ directory in the psad sources, and are automatically installed by the install.pl script. The list of modules is:
- Bit::Vector
- Date::Calc
- IPTables::ChainMgr
- IPTables::Parse
- NetAddr::IP
- Storable
- Unix::Syslog
psad also includes a whois client written by Marco d’Itri (see the deps/whois directory). This client does better than others at collecting the correct whois information for a given IP address.
Firewall Setup
The main requirement for an iptables configuration to be compatible with psad is simply that iptables logs packets. This is commonly accomplished by adding rules to the INPUT and FORWARD chains like so:
iptables -A INPUT -j LOG
iptables -A FORWARD -j LOG
The rules above should be added at the end of the INPUT and FORWARD chains after all ACCEPT rules for legitimate traffic and just before a corresponding DROP rule for traffic that is not to be allowed through the policy. Note that iptables policies can be quite complex with protocol, network, port, and interface restrictions, user defined chains, connection tracking rules, and much more. There are many pieces of software such as Shorewall and Firewall Builder, that build iptables policies and take advantage of the advanced filtering and logging capabilities offered by iptables. Generally the policies built by such pieces of software are compatible with psad since they specifically add rules that instruct iptables to log packets that are not part of legitimate traffic. Psad can be configured to only analyze those iptables messages that contain specific log prefixes (which are added via the –log-prefix option), but the default is for psad to analyze all iptables log messages for evidence of port scans, probes for backdoor programs, and other suspect traffic.
Download
![]()

0 Comments