Fluxion
Hack WPA/WPA2 Security Without Brute Force
Fluxion script has been available for a while and is most apt for security researchers and pentesters to test their network security by hacking WPA/WPA2 security without brute forcing it. Fluxion is based on another script called linset. Fluxion is not much different from Linset but makes use of certain improvements, bug fixes, and additional features. Fluxion works by using something like a man in the middle attack/ evil twin attack to get WPA password instead of going the bruteforce/dictionary route.
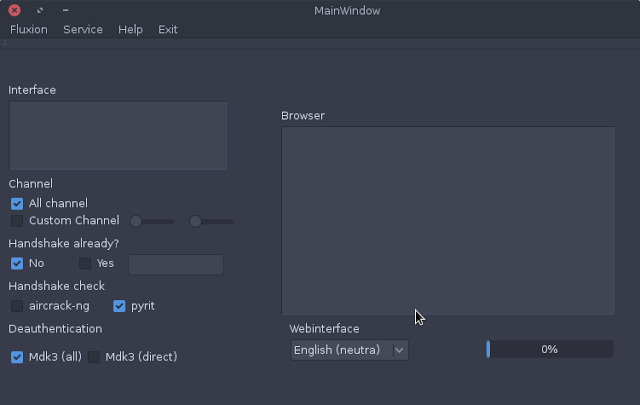
Fluxion is compatible with the latest release of Kali (Rolling). Latest builds (stable) and (beta) here. Kindly read the Fluxion Wiki to get the full tutorial.
How it works:
Step 1: Scan the networks.
Step 2: Capture a handshake (can’t be used without a valid handshake, it’s necessary to verify the password)
Step 3: Use WEB Interface *
Step 4: Launch a FakeAP instance to imitate the original access point
Step 5: Spawns a MDK3 process, which deauthenticates all users connected to the target network, so they can be lured to connect to the FakeAP and enter the WPA password.
Step 6: A fake DNS server is launched in order to capture all DNS requests and redirect them to the host running the script
Step 7: A captive portal is launched in order to serve a page, which prompts the user to enter their WPA password
Step 8: Each submitted password is verified by the handshake captured earlier
Step 9: The attack will automatically terminate, as soon as a correct password is submitted
Requirements:
- Linux operating system
- Kali Linux 2 or Kali 2016.1 rolling or
- Kali 2 & 2016 support the latest Aircrack-ng versions
- External Wi-Fi card is recommended
Disclaimer:
Use this tool only on networks you own. Hacking networks that you don’t own may be illegal in your country.
![]()