Vulnerability Exploitation Tool
What is Metasploit?
In 2003, H.D. Moore, (a Cyber Security Researcher and Program Developer from the US) started the Metasploit Project with the intention being to create a public and freely accessible resource to obtain exploitable code for research and development. The Metasploit Project is credited with the creation of the Metasploit Framework, which has become an open-source exploit framework used for IT Security penetration testing and research.
In 2009, Metasploit was acquired by Rapid7, but was still managed by HD until 2013 when he handed management of the Metasploit department in order to expand Rapid7’s research capabilities.
Is Metasploit Free?
Yes and no…the Metasploit Framework is free and can be downloaded here. Since the tool was acquired by Rapid7 there are two core proprietary editions called Metasploit Pro and Metasploit Express. If you’re new to pentesting and are looking to get started in Cyber Security then we’d highly encourage you to get started with the Metasploit Framework because you’ll absolutely learn a ton.
What’s the Difference between Metasploit Framework and Metasploit Pro Framework?
Whilst Metasploit Framework is free, its’ functionality is relatively basic. Professional security researchers, pentesters and ethical hackers would likely prefer to use Metasploit Pro which is the fully-fledged security solution for security programs and advanced penetration tests for SME’s and enterprise level organizations. Measploit Pro would be used for in-depth IT security auditing.
What Are Vulnerability Exploitation Tools?
Metasploit can be categorized in many ways, but we here at concise like to place this tool, or perhaps better said, ‘Framework’, as being a Vulnerability Exploitation Tool. Vulnerability Exploitation Tools are mainly used to discover if an attacker could find overflow weakness to install malware, or to discover fundamental operating and network system design flaws.
Does Metasploit Work on all Operating Systems?
Metasploit runs on Unix (including Linux and Mac OS X) and on Windows, and the Metasploit Framework has been translated in verbose to dozens of languages.
Step 1: Choosing and configuring an exploit code
This step requires the professional to select code with the purpose of being able to penetrate a target system by taking advantage of a ‘vulnerability’ that is inherently embedded in the target box or network. Metasploit can pull nearly 1,000 exploits for Windows, Unix/Linux and Mac OS X systems
Step 2: Checking the Target
This step allows the hacker to discover with more accuracy if the target is penetrable with the chosen exploit. If not, then select another!
Step 3: Select and configure a payload to send to the target.
This could include, for instance, a remote shell or a VNC server.
Step 4: Get around the IDS/ IPS system (Intruston Detection System)
This step is all about using Metasploit to encode and encrypt the attack to essential go ‘under the radar.’
Step 5: Executing the exploit
This final step is all about the final and actual hack that can either pwn a box or network and be able to remove data or deface a website.
Installing Metasploit Framework
We will download the latest version of Metasploit Framework via Git so we can use msfupdate to keep it updated:
cd /opt sudo git clone https://github.com/rapid7/metasploit-framework.git sudo chown -R `whoami` /opt/metasploit-framework cd metasploit-framework
Install using bundler the required gems and versions:
cd metasploit-framework
# If using RVM set the default gem set that is create when you navigate in to the folder
rvm --default use ruby-${RUByVERSION}@metasploit-framework
gem install bundler
bundle install
Lets create the links to the commands so we can use them under any user and not being under the framework folder, for this we need to be in the metasploit-framework folder if not already in it:
cd metasploit-framework sudo bash -c 'for MSF in $(ls msf*); do ln -s /opt/metasploit-framework/$MSF /usr/local/bin/$MSF;done'
Metasploit for Development and Contribution
If you wish to develop and contribute to the product you can follow the additional steps here Metasploit Dev Environment . For this you will need a GitHub account and you will fork the project in to your own account. I personally keep my dev copy of Metasploit in ~/Development folder and after an initial run of msfconsole I keep my database.yml file in ~/.msf4/cofig folder and adjust the MSF_DATABASE_CONFIG variable for it or run msfconsole with the -y option and point it to a YAML file with the correct configuration.
Installing armitage:
curl -# -o /tmp/armitage.tgz http://www.fastandeasyhacking.com/download/armitage150813.tgz sudo tar -xvzf /tmp/armitage.tgz -C /opt sudo ln -s /opt/armitage/armitage /usr/local/bin/armitage sudo ln -s /opt/armitage/teamserver /usr/local/bin/teamserver sudo sh -c "echo java -jar /opt/armitage/armitage.jar \$\* > /opt/armitage/armitage" sudo perl -pi -e 's/armitage.jar/\/opt\/armitage\/armitage.jar/g' /opt/armitage/teamserver
Lets create the database.yml file that will contain the configuration parameters that will be use by framework:
sudo nano /opt/metasploit-framework/config/database.yml
Copy the YAML entries and make sure you provide the password you entered in the user creating step in the password field for the database:
production: adapter: postgresql database: msf username: msf password: host: 127.0.0.1 port: 5432 pool: 75 timeout: 5
Create and environment variable so it is loaded by Armitage and by msfconsole when running and load the variable in to your current shell:
sudo sh -c "echo export MSF_DATABASE_CONFIG=/opt/metasploit-framework/config/database.yml >> /etc/profile" source /etc/profile
First Run
Now we are ready to run Metasploit for the first time. My recommendation is to run it first under a regular user so the folders create under your home directory have the proper permissions. First time it runs it will create the entries needed by Metasploit in the database so it will take a while to load.
msfconsole
Basic Msfconsole commands
Assuming you are on Kali Linux 2016 rolling edition we can start the Metasploit framework and msfconsole by clicking the Metasploit icon in the dock. This will start the PostgreSQL service and Metasploit service automatically.
Updating Metasploit with msfupdate
Let’s start with updating Metasploit by using the following command in a terminal session (not in msfconsole):
msfupdate
This command should update the Metasploit framework to the latest version. The updates says that we should be expecting updates weekly(ish). Beware: Running msfupdate might break your Metasploit installation. After running this command for this tutorial we ran into errors like:
An error occurred while installing pg (0.18.3), and Bundler cannot continue.
Make sure that gem install pg -v '0.18.3' succeeds before bundling.
This error had something to do with PostgreSQL and to fix this problem first try to run the following commands:
apt-get update
apt-get upgrade
apt-get dist-upgrade
This solved to problem on our side, it probably had something to do with an outdated version of a package. Is your Metasploit installation broken after running an update and you need some help to fix it? Use the comment function below and we’ll try to help you as best as we can. Let’s continue with the msfconsole.
Metasploit msfconsole
When Metasploit has booted and the msfconsole is available we can type ‘help’ to get an overview of the Metasploit core and backend commands with a description:

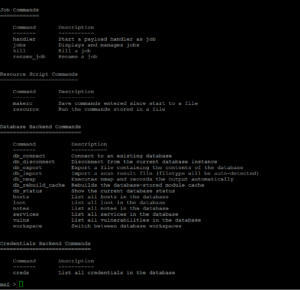
It would be a waste of time and outside the scope of this tutorial to explain every single Metasploit command in this tutorial. We just want you to be up and running as soon as possible in Metasploit and therefore a basic knowledge of basics commands should be sufficient for the moment. You will learn a lot more about the advanced options along the way. Also, most command descriptions should be very clear about what the command exactly does and how to use it. For now we will be looking at the most used basic Metasploit commands in this tutorial like:
- Basic commands: search, use, back, help, info and exit.
- Exploit commands: set to set variables and show to show the exploit options, targets, payloads, encoders, nops and the advanced and evasion options.
- Exploit execution commands: run and exploit to run exploits against a target.
There is also a comprehensive Metasploit documentation included with Metasploit which can be used to clarify anything. Let’s have a look at the Metasploit commands.
Metasploit commands
We will go through the Metasploit basic commands quickly so we can get started with the fun part and learn how to use the exploits on a vulnerable machine like Metasploitable 2. The basics command consist of help, back, exit and info.
Use, back and exit commands
The use command in Metasploit is used to activate a particular module and changes the context of the msfconsole to that particular module. The exploit name will be mentioned in red on the command line as following:

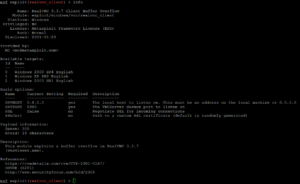
In this example we have changed the context of the command line to the exploit called realvnc_client. From here on we can retrieve information about this exploit, set the required exploit parameters and run it against a target.
If we want to leave the exploit context and switch back to the msfconsole we need to use the back command. The back command will take us back to the msfconsole in the general context. From here on we can issue the use command again to switch to another Metasploit module.
The exit command will close the msfconsole and will take you back to the Kali Linux terminal.
Help command
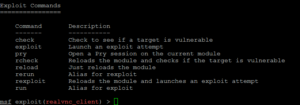
As we’ve seen earlier in this tutorial the help command will return a list of possible commands together with a description when typed at the msfconsole. When there is an active exploit selected we can use the help command to get a list of exploit commands:
Info command
When an exploit is selected with the use command we can retrieve information like the name, platform, author, available targets and a lot more by using the info command. In the following screenshot we’ve use the info command on an exploit named realvnc_client:
Search command
As of this writing Metasploit contains over 1.500 different exploits and new ones are added regularly. With this number of exploit the search function, and knowing how to use it, becomes very important. The easiest way of using the search function is by issuing the command search followed by a search term, for example flash to search for exploits related to Flash player. By using the search command Metasploit will search for the given search term in the module names and description as following:

Searching with exploits with keywords
You can also use the search command with a keyword to search for a specific author, an OSVDB ID or a platform. The ‘help search’ command displays the available keywords in the msfconsole as following:
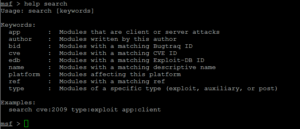
The usage of the search command with a keyword is pretty straight forward and displayed at the bottom of the help text. The following command is used to search for modules with a CVE ID from 2016:
msf > search cve:2016
This returns us all exploits with a CVE ID from 2016 including and auxiliary module scanner for the very recent Fortinet firewall SSH backdoor:

Metasploit commands for exploits
In the previous chapter we’ve learned the Metasploit commands to activate an exploit on the msfconsole and change the command line context to the exploit with the use command. Now we will be looking at how to show the exploit parameters and how to change them with the set command. We will also be looking at how to show the payloads, targets, advanced and evasion options. The help show command will display the available parameters for the show command:
![]()
Show options
The show options command will show you the available parameters for an exploit if used when the command line is in exploit context. Let’s use the adobe_flash_shader_drawing_fill exploit and have a look at the options with the following command:
msf > Use exploit/multi/browser/ adobe_flash_shader_drawing_fill
Followed by the show options command:
msf > show options

The Flash exploit contains a total of 6 options from which only 2 are required:
- Retries
- SRVHOST (Required)
- SRVPORT (Required)
- SSL
- SSLCert
- URLPath
Note that the show options command is returning the current selected target below the module options. The default target is 0 which is Windows for the selected exploit.
Use the set command followed by the option name and the new value to change the default values:
Set SRVHOST 192.168.0.107 to change the SRVHOST value to 192.168.0.107
Set SRVPORT 80 to change the port from 8080 to 80

By using the show options command again you can verify that the SRVHOST and SRVPORT values have been changed. You can change Boolean values by using the set command with option name and true or false.
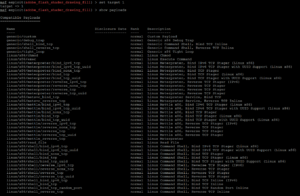
Show payloads
When we use the show payloads command the msfconsole will return a list of compatible payloads for this exploit. In our flash player exploit example it will return quite a few compatible payloads:

To use a certain payload you need to use the set command followed by the payload name:
set payload linux/x86/exec
![]()
Show targets
The show targets command will return a list of operating systems which are vulnerable to the selected exploit. When we run the command we get the following output for the adobe_flash_shader_drawing_fill exploit:
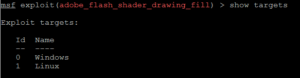
This exploit targets both Windows and Linux operating systems. Note that we can use the info command to get additional info about this exploit and targets.
To set a target we can use the command set followed by the target ID:
set target 1
By setting the target the list of payloads will be reduced a lot because only payloads will be shown which are compatible with the target:
Show advanced
By using the show advanced command we can have a look at the advanced options for the exploit.

Use the set command followed by the advanced parameter and the new value to change the advanced settings:
Set displayablepayloadhandler true

Show encoders
The show encoders command will return the compatible encoders. Encoders are used to evade simple IDS/IPS signatures that are looking for certain bytes of your payload.
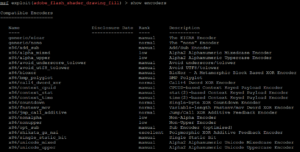
To use an encoder use the set command followed by the name of the encoder.
Show nops
The show nops command will return a list of NOP generators. A NOP is short for No Operation and is used to change the pattern of a NOP sled in order to bypass simple IDS/IPS signatures of common NOP sleds. The NOP generators start with the CPU architecture in the name.
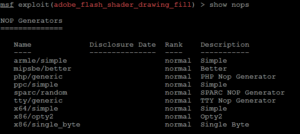
To use a NOP generator use the set command followed by the name of the NOP generator. When the exploit is launched the NOP sleds will be taken from the NOP generator.
Show evasion
The show evasion command returns a list of available evasion techniques.

To change evasions settings use the set command followed by the evasion parameter and the new value.
Metasploit commands for exploit execution
When all the required options have been set for the exploit, including a payload and advanced settings like a NOP generator, evasion options and encoding, the exploit is ready to be executed. The exploit can be executed using two commands: run or exploit. Just type run or exploit in the msfconsole and the exploit will run.
This will conclude the Metasploit commands tutorial for now.
![]()

